[Editor’s Note: Mad Scientist Laboratory is pleased to publish today’s guest blog post by Mr. Alexander Temerev addressing the possible democratization and proliferation of nuclear weapons expertise, currently residing with only a handful of nation states (i.e., the U.S., Russia, China, the UK, France, India, Pakistan, and North Korea). We vetted this post with nuclear subject matter experts within our community of action (who wish to remain anonymous) – the following initial comments are their collective input regarding Mr. Temerev’s guest post that follows – read on!]
What is proposed below “is not beyond the realm of possibility and, with enough wise investment, rather feasible — there are no secrets left in achievement of the basic nuclear physics package, and there haven’t been for a while (the key being obtaining the necessary fissile material). A side note — I was a friend and school-mate of the apocryphal Princeton University Physics Undergraduate Student in  1978 who, as part of his final degree project, developed a workable nuclear weapons design with nothing more than the pre-Internet Science Library as a resource. They still talk about the visit from the FBI on campus, and the fact that his professor only begrudgingly gave him an A- as a final grade.”
1978 who, as part of his final degree project, developed a workable nuclear weapons design with nothing more than the pre-Internet Science Library as a resource. They still talk about the visit from the FBI on campus, and the fact that his professor only begrudgingly gave him an A- as a final grade.”
“Considering the advances since then, it’s likewise no surprise that such a thing could be accomplished today with even greater ease, there remaining the issue of obtaining sufficient fissile material to warrant the effort. Of course, even failure in this regard, done artfully, could still accomplish a sub-critical reaction [aka “a fizzle“– an explosion caused by the two sub-critical masses of the bomb being brought together too slowly] resulting in a militarily (and psychologically) effective 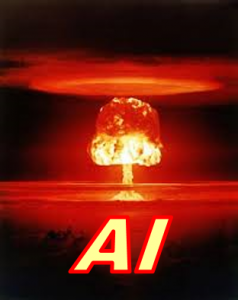 detonation. So, as my colleague [name redacted] (far more qualified in matters scientific and technical) points out, with the advances since the advent of the Internet and World Wide Web, the opportunity to obtain the ‘Secret Sauce’ necessary to achieve criticality have likewise advanced exponentially. He has opined that it is quite feasible for a malevolent private actor, armed with currently foreseeable emerging capabilities, to seek and achieve nuclear capabilities utilizing Artificial Intelligence (AI)-based data and communications analysis modalities. Balancing against this emerging capability are the competing and ever-growing capabilities of the state to surveil and discover such endeavors and frustrate them before (hopefully) reaching fruition. Of course, you’ll understand if I only allude to them in this forum and say nothing further in that regard.”
detonation. So, as my colleague [name redacted] (far more qualified in matters scientific and technical) points out, with the advances since the advent of the Internet and World Wide Web, the opportunity to obtain the ‘Secret Sauce’ necessary to achieve criticality have likewise advanced exponentially. He has opined that it is quite feasible for a malevolent private actor, armed with currently foreseeable emerging capabilities, to seek and achieve nuclear capabilities utilizing Artificial Intelligence (AI)-based data and communications analysis modalities. Balancing against this emerging capability are the competing and ever-growing capabilities of the state to surveil and discover such endeavors and frustrate them before (hopefully) reaching fruition. Of course, you’ll understand if I only allude to them in this forum and say nothing further in that regard.”
“Nonetheless, for both good guy and bad, given enough speed and capacity, these will serve as the lever to move the incorporeal data world. This realization will move the quiet but deadly arms race in the shadows, that being the potential confluence of matured Artificial Intelligence (AI) and Quantum technologies at a point in the foreseeable future that changes everything. Such a confluence would enable the potential achievement of these, and even worse, WMD developmental approaches through big-data analysis currently considered infeasible. Conversely, state surveillance modes of the Internet would likewise profit through identifying clusters of seemingly unrelated data searches that could be analyzed to identify and frustrate malevolent actors”.
 “It is quite conceivable, in this context, that the future of the Internet for our purposes revolves around one continuous game of cat and mouse as identities are sought and hidden between white hat and black hat players. A real, but unanticipated, version of Ray Kurtzweil’s singularity that nonetheless poses fundamental challenges for a free society. In the operational environment to 2050, cyber-operations will no longer be a new domain but one to be taken into account as a matter of course.”
“It is quite conceivable, in this context, that the future of the Internet for our purposes revolves around one continuous game of cat and mouse as identities are sought and hidden between white hat and black hat players. A real, but unanticipated, version of Ray Kurtzweil’s singularity that nonetheless poses fundamental challenges for a free society. In the operational environment to 2050, cyber-operations will no longer be a new domain but one to be taken into account as a matter of course.”
“Once again, all credit goes to [my colleague] for providing the technical insight into this challenge, my contribution being entirely eccentric in nature. I believe the blog is worth publishing, provided that it serves as an opening for furthering discussion of the potential long-range implications such developments would pose.”
A Scenario for a Hypothetical Private Nuclear Program
Let’s assume there is a non-government actor willing to acquire nuclear weapons for some reason. Assume that the group has unlimited financing (or some significant amount of free and untraced money available — e.g., $1 billion in cryptocurrencies). What would be the best way for them to proceed, and what would be the most vulnerable points where they could be stopped?
Stealing existing nuclear weapons would probably not be an option (or will be of limited utility — see below). Modern nuclear devices are all equipped with PALs (permissive action links), rendering them unusable without unlocking codes (the key idea of PAL is removing some small amount of explosives from the implosion shell, different for each detonator – and compensating by adjusting precise timings when each detonator goes off; these timings are different for each device and can be released only by central command authority). Without knowing the entire set of PAL timings and the entire encrypted protocol between PAL controller and detonators, achieving a bona fide nuclear explosion is technically impossible. Some countries like Pakistan and perhaps North Korea do not possess sophisticated PAL systems for their devices; to compensate, their nuclear cores are tightly guarded by the military.

Therefore, even if weapon-grade nuclear materials are available (which is of course another near impossible problem), designing the nuclear explosive device de novo is still unavoidable. The principal design of nuclear weapons is not secret, and achieving the nuclear explosion is a clearly defined problem (in terms of timing, compression and explosion hydrodynamics) that can be solved by a small group of competent physicists. Indeed, the “Nth Country Experiment” by Lawrence Livermore National Laboratory in 1964 has shown that three bright physicists (without previous nuclear expertise) can deliver a plausible design for a working nuclear weapon (they were building an analogue of the Fat Man device, which is bulky and nearly undeliverable; today, more compact options should be pursued instead). A heavily redacted report is available online.
With modern computers, open information about nuclear weapons, some OSINT, and determination, the same feat could probably be accomplished in less than a year. (Some open source software and libraries that can be useful in such an endeavor, e.g., Castro for explosion hydrodynamics; there is also a guidebook for anyone with a deep interest in the field.) Many ideas for the critical part of the device – the neutron initiator — are also discussed in the open literature (here I will refrain from mentioning exact books and papers, but the information is still publicly available). Again, the task is clearly formulated — injecting the neutrons at the very precise moment during the explosion — this is only an engineering problem.
 Assembling the device itself is no easy task; it requires precision engineering and the casting of high explosives, which cannot be done without significant pre-existing expertise. However, the brightest mechanical engineers and even explosives technicians can be legally hired on the open market, if not for the direct participation in the project, then for training and knowledge transfer for the project team. Private organizations have achieved even more complicated engineering feats (e.g., rocket engines at SpaceX), so this part looks feasible.
Assembling the device itself is no easy task; it requires precision engineering and the casting of high explosives, which cannot be done without significant pre-existing expertise. However, the brightest mechanical engineers and even explosives technicians can be legally hired on the open market, if not for the direct participation in the project, then for training and knowledge transfer for the project team. Private organizations have achieved even more complicated engineering feats (e.g., rocket engines at SpaceX), so this part looks feasible.
All current nuclear devices require periodic maintenance and re-casting of their plutonium pits with additional weapon-grade plutonium added every few years; otherwise their neutronic profile will gradually become too unfavorable to achieve a full nuclear explosion. If the group has acquired nuclear materials by stealing them, they will have to make use of them during the following few years. Nuclear programs of sovereign states, of course, have the entire weapon-grade plutonium production pipelines at their disposal, so the fresh plutonium is always available. This will be a much harder feat to achieve for a non-state actor. Ironically, the plutonium could be provided by disassembling PAL-equipped stolen or captured nuclear devices, which are less heavily guarded. While it is true that PAL will prevent their full scale explosion, they still can be the priceless source of weapon-grade plutonium.

Conclusion: Safeguarding weapon-grade nuclear materials is the highest priority, as the design details of nuclear devices are hardly a secret these days, and can be readily reproduced by many competent and determined organizations. Emergence of nuclear production pipelines (isotope separation, SILEX [Separation of Isotopes by Laser Excitation], plutonium separation, plutonium-producing reactors) should be monitored everywhere. Even PAL-equipped weapons need to be closely guarded, as they can be the sources of these materials. Groups and non-state actors willing to acquire nuclear capabilities without building the full production pipeline need to act fast and have the design and device prototypes (sans cores) ready before acquiring nuclear materials, as their utility is diminishing every year since acquisition.
If you enjoyed this post, please also see:
-
- A New Age of Terror: The Future of CBRN Terrorism, and A New Age of Terror: New Mass Casualty Terrorism Threats, by Zachary Kallenborn
- The Democratization of Dual Use Technology
- Emergent Threat Posed by Super-Empowered Individuals
- Blurred Lines and Super-Empowered Individuals: Is National Security Still Possible in 2040? presented by Dr. David Bray at the Mad Scientist Visioning Multi Domain Battle in 2030-2050 Conference at Georgetown University, Washington, D.C., 25 July 2017.
REMINDER: Don’t forget to join us tomorrow on-line at the Mad Scientist GEN Z and the OE Livestream Event! This event is open to all, on any device, anywhere (but is best streamed via a commercial, non-DoD network) — plan on joining us at 1330 EST on 21 February 2020 at: www.tradoc.army.mil/watch and engage in the discussion by submitting your questions and comments via this site’s moderated interactive chat room. You can also follow along on Twitter @ArmyMadSci. For more information, click here!
ALSO: Help Mad Scientist expand the U.S. Army’s understanding of the Operational Environment (OE) — join the 662 others representing 46 nations who have already done so and take a few minutes to complete  our short, on-line Global Perspectives Survey. Check out our initial findings here and stay tuned to future blog posts on the Mad Scientist Laboratory to learn what further insights we will have gleaned from this survey about OE trends, challenges, technologies, and disruptors.
our short, on-line Global Perspectives Survey. Check out our initial findings here and stay tuned to future blog posts on the Mad Scientist Laboratory to learn what further insights we will have gleaned from this survey about OE trends, challenges, technologies, and disruptors.
FINALLY: Don’t forget to enter The Operational Environment in 2035 Mad Scientist Writing Contest and share your unique insights on the future of warfighting — click here to learn more (submission deadline is 1 March 2020!)
Mr. Alexander Temerev is a consultant in complex systems dynamics and network analysis; he is CEO and founder of Reactivity – a boutique consulting company in Geneva, Switzerland.
Disclaimer: The views expressed in this blog post do not necessarily reflect those of the Department of Defense, Department of the Army, Army Futures Command (AFC), or the Training and Doctrine Command (TRADOC).


 Ethnic Russian minorities’ agitation against their respective governments in Estonia, Lithuania, and Latvia spike. Simultaneously, the Russian Government ratchets up tensions, with inflammatory statements of support for these ethnic Russian minorities in the Baltic States; coordinated movements and exercises by Russian ground, naval, and air forces adjacent to the region; and clandestine support to ethnic Russians in these States. The Russian Government started a covert campaign to shape people’s views about the threats against the Russian diaspora. More than 200,000 twitter accounts send 3.6 million tweets trending #protectRussianseverywhere. This sprawling Russian disinformation campaign is focused on building internal support for the Russian President and a possible military action. The U.S. and NATO respond…
Ethnic Russian minorities’ agitation against their respective governments in Estonia, Lithuania, and Latvia spike. Simultaneously, the Russian Government ratchets up tensions, with inflammatory statements of support for these ethnic Russian minorities in the Baltic States; coordinated movements and exercises by Russian ground, naval, and air forces adjacent to the region; and clandestine support to ethnic Russians in these States. The Russian Government started a covert campaign to shape people’s views about the threats against the Russian diaspora. More than 200,000 twitter accounts send 3.6 million tweets trending #protectRussianseverywhere. This sprawling Russian disinformation campaign is focused on building internal support for the Russian President and a possible military action. The U.S. and NATO respond… The 2nd Cav Regt is placed on alert; as it prepares to roll out of garrison for Poland, several videos surface across social media, purportedly showing the sexual assault of several underage German nationals by U.S. personnel. These disturbingly graphic
The 2nd Cav Regt is placed on alert; as it prepares to roll out of garrison for Poland, several videos surface across social media, purportedly showing the sexual assault of several underage German nationals by U.S. personnel. These disturbingly graphic  the Regiment. German political and legal authorities call for an investigation and host nation protests erupt outside the gates of Rose Barracks, Vilseck, disrupting the unit’s deployment.
the Regiment. German political and legal authorities call for an investigation and host nation protests erupt outside the gates of Rose Barracks, Vilseck, disrupting the unit’s deployment. Social media accounts are hacked/hijacked, with false threats by dependents to execute mass/school shootings, accusations of sexual abuse, hate speech posts by Leaders about their minority troops, and revelations of adulterous affairs between unit spouses.
Social media accounts are hacked/hijacked, with false threats by dependents to execute mass/school shootings, accusations of sexual abuse, hate speech posts by Leaders about their minority troops, and revelations of adulterous affairs between unit spouses. Russia’s GRU (Military Intelligence) employs AI Generative Adversarial Networks (GANs) to create fake persona injects that mimic select U.S. Active Army, ARNG, and USAR commanders making disparaging statements about their confidence in our allies’ forces, the legitimacy of the mission, and their faith in our political leadership. Sowing these injects across unit social media accounts, Russian Information Warfare specialists seed doubt and erode trust in the chain of command amongst a percentage of susceptible Soldiers, creating further friction in deployment preparations.
Russia’s GRU (Military Intelligence) employs AI Generative Adversarial Networks (GANs) to create fake persona injects that mimic select U.S. Active Army, ARNG, and USAR commanders making disparaging statements about their confidence in our allies’ forces, the legitimacy of the mission, and their faith in our political leadership. Sowing these injects across unit social media accounts, Russian Information Warfare specialists seed doubt and erode trust in the chain of command amongst a percentage of susceptible Soldiers, creating further friction in deployment preparations. As these units load at railheads or begin their road march towards their respective ports of embarkation,
As these units load at railheads or begin their road march towards their respective ports of embarkation,  navigation systems to cause sealift asset collisions and groundings at key maritime chokepoints. The fly-by-wire avionics are hacked on a departing C-17, causing a crash with the loss of all 134 Soldiers onboard. All C-17s are grounded, pending an investigation.
navigation systems to cause sealift asset collisions and groundings at key maritime chokepoints. The fly-by-wire avionics are hacked on a departing C-17, causing a crash with the loss of all 134 Soldiers onboard. All C-17s are grounded, pending an investigation. the alliance for the Multi-Domain Common Operating Picture. Spoofing of these systems leads to accidental air defense engagements, resulting in Blue-on-Blue fratricide or the downing of a commercial airliner, with additional civilian deaths on the ground from spent ordnance, providing more opportunities for Russian Information Operations to spread acrimony within the alliance and create dissent in public opinion back home.
the alliance for the Multi-Domain Common Operating Picture. Spoofing of these systems leads to accidental air defense engagements, resulting in Blue-on-Blue fratricide or the downing of a commercial airliner, with additional civilian deaths on the ground from spent ordnance, providing more opportunities for Russian Information Operations to spread acrimony within the alliance and create dissent in public opinion back home. across the net via bots, these instances further stoke anti-Baltic / anti-U.S. opinion amongst Russian-sympathetic and non-aligned populations alike.
across the net via bots, these instances further stoke anti-Baltic / anti-U.S. opinion amongst Russian-sympathetic and non-aligned populations alike. The release of deepfake videos showing Baltic security forces massacring ethnic Russians creates further division and causes some NATO partners to hesitate, question, and withhold their support, as required under Article 5. The alliance is rent asunder — Checkmate!
The release of deepfake videos showing Baltic security forces massacring ethnic Russians creates further division and causes some NATO partners to hesitate, question, and withhold their support, as required under Article 5. The alliance is rent asunder — Checkmate!
 mirror imaging. The Mad Scientist Laboratory offers it as a platform for the contrarians in our network to share their alternative perspectives and analyses regarding the Operational Environment (OE). We continue our series of “Tenth Man” posts examining the foundational assumptions of
mirror imaging. The Mad Scientist Laboratory offers it as a platform for the contrarians in our network to share their alternative perspectives and analyses regarding the Operational Environment (OE). We continue our series of “Tenth Man” posts examining the foundational assumptions of The character of warfare will change in the future OE as it inexorably has since the advent of flint hand axes; iron blades; stirrups; longbows; gunpowder; breech loading, rifled, and automatic guns; mechanized armor; precision-guided munitions; and the Internet of Things. Speed, automation, extended ranges,
The character of warfare will change in the future OE as it inexorably has since the advent of flint hand axes; iron blades; stirrups; longbows; gunpowder; breech loading, rifled, and automatic guns; mechanized armor; precision-guided munitions; and the Internet of Things. Speed, automation, extended ranges,  broad and narrow weapons effects, and increasingly integrated multi-domain conduct, in addition to the complexity of the terrain and social structures in which it occurs, will make mid Twenty-first Century warfare both familiar and utterly alien.
broad and narrow weapons effects, and increasingly integrated multi-domain conduct, in addition to the complexity of the terrain and social structures in which it occurs, will make mid Twenty-first Century warfare both familiar and utterly alien. assumes that humans will remain central to the rationale for war and its most essential elements of execution. The nature of war has remained relatively constant from Thucydides through Clausewitz, and forward to the present. War is still waged because of fear, honor, and interest, and remains an expression of politics by other means. While machines are becoming ever more prevalent across the battlefield – C5ISR, maneuver, and logistics – we cling to the belief that parties will still go to war over human interests; that war will be decided, executed, and controlled by humans.
assumes that humans will remain central to the rationale for war and its most essential elements of execution. The nature of war has remained relatively constant from Thucydides through Clausewitz, and forward to the present. War is still waged because of fear, honor, and interest, and remains an expression of politics by other means. While machines are becoming ever more prevalent across the battlefield – C5ISR, maneuver, and logistics – we cling to the belief that parties will still go to war over human interests; that war will be decided, executed, and controlled by humans. Imagine that a machine recognizes a strategic opportunity or impetus to engage a nation-state actor that is conventionally (read that humanly) viewed as weak or in a presumed disadvantaged state. The machine launches offensive operations to achieve a favorable outcome or objective that it deemed too advantageous to pass up.
Imagine that a machine recognizes a strategic opportunity or impetus to engage a nation-state actor that is conventionally (read that humanly) viewed as weak or in a presumed disadvantaged state. The machine launches offensive operations to achieve a favorable outcome or objective that it deemed too advantageous to pass up. influence may not be conducive to victory. Victory may be simply a calculated or algorithmic outcome that causes an adversary’s machine to decide their own victory is unattainable.
influence may not be conducive to victory. Victory may be simply a calculated or algorithmic outcome that causes an adversary’s machine to decide their own victory is unattainable. – How much and how should the Army recruit and cultivate human talent if war is no longer human-centric?
– How much and how should the Army recruit and cultivate human talent if war is no longer human-centric? – Should the U.S. military divest from platforms and materiel solutions (hardware) and re-focus on becoming algorithmically and digitally-centric (software)?
– Should the U.S. military divest from platforms and materiel solutions (hardware) and re-focus on becoming algorithmically and digitally-centric (software)? – Technology advances to the point of near or actual machine sentience, with commensurate machine speed accelerating the potential for escalated competition and armed conflict beyond transparency and human comprehension.
– Technology advances to the point of near or actual machine sentience, with commensurate machine speed accelerating the potential for escalated competition and armed conflict beyond transparency and human comprehension. – Smaller, less-capable states or actors begin achieving surprising or unexpected victories in warfare.
– Smaller, less-capable states or actors begin achieving surprising or unexpected victories in warfare.
 A loud buzz pierced the quiet night air. A group of drones descended on a chemical plant near New York City. The drones disperse throughout the installation in search of storage tanks. A few minutes later, the buzz of the drone propellers was drowned out by loud explosions. A surge of fire leapt to the sky. A plume of gas followed, floating towards the nearby city. The gas killed thousands and thousands more were hospitalized with severe injuries.
A loud buzz pierced the quiet night air. A group of drones descended on a chemical plant near New York City. The drones disperse throughout the installation in search of storage tanks. A few minutes later, the buzz of the drone propellers was drowned out by loud explosions. A surge of fire leapt to the sky. A plume of gas followed, floating towards the nearby city. The gas killed thousands and thousands more were hospitalized with severe injuries.  Drones offer terrorists low cost methods of delivering harm with lower risk to attacker lives. Drone attacks can be launched from afar, in a hidden position, close to an escape route. Simple unmanned systems can be acquired easily: Amazon.com offers seemingly hundreds of drones for as low as $25. Of course, low cost drones also mean lower payloads that limit the harm caused, often significantly. Improvements to drone autonomy will allow terrorists to deploy more drones at once, including in true drone swarms.
Drones offer terrorists low cost methods of delivering harm with lower risk to attacker lives. Drone attacks can be launched from afar, in a hidden position, close to an escape route. Simple unmanned systems can be acquired easily: Amazon.com offers seemingly hundreds of drones for as low as $25. Of course, low cost drones also mean lower payloads that limit the harm caused, often significantly. Improvements to drone autonomy will allow terrorists to deploy more drones at once, including in true drone swarms. oil production capacity.
oil production capacity. potential still exists for significant harm. Terrorists can strike popular tourist sites like the Statue of Liberty or San Francisco’s Fisherman’s Wharf. U.S. military vessels are ideal targets too, such as the USS Cole bombing in October 2000.
potential still exists for significant harm. Terrorists can strike popular tourist sites like the Statue of Liberty or San Francisco’s Fisherman’s Wharf. U.S. military vessels are ideal targets too, such as the USS Cole bombing in October 2000. aroochy Shire, Australia, and released hundreds of thousands of gallons of raw sewage into the surrounding area.
aroochy Shire, Australia, and released hundreds of thousands of gallons of raw sewage into the surrounding area.