[Editor’s Note: In today’s post, Mad Scientist Laboratory explores China’s whole-of-nation approach to exploiting operational environments, synchronizing government, military, and industry activities to change geostrategic power paradigms via competition in 2035. Excerpted from products previously developed and published by the TRADOC G-2’s Operational Environment and Threat Analysis Directorate (see links below), this post describes China’s approach to exploitation and identifies the implications for the U.S. Army — Enjoy!]
 The Operational Environment is envisioned as a continuum, divided into two eras: the Era of Accelerated Human Progress (now through 2035) and the Era of Contested Equality (2035 through 2050). This latter era is marked by significant breakthroughs in technology and convergences in terms of capabilities, which lead to significant changes in the character of warfare. During this period, traditional aspects of warfare undergo dramatic, almost revolutionary changes which at the end of this timeframe may even challenge the very nature of warfare itself. In this era, no one actor is likely to have any long-term strategic or technological advantage, with aggregate power between the U.S. and its strategic competitors being equivalent, but not necessarily symmetric. Prevailing in this period will depend on an ability to
The Operational Environment is envisioned as a continuum, divided into two eras: the Era of Accelerated Human Progress (now through 2035) and the Era of Contested Equality (2035 through 2050). This latter era is marked by significant breakthroughs in technology and convergences in terms of capabilities, which lead to significant changes in the character of warfare. During this period, traditional aspects of warfare undergo dramatic, almost revolutionary changes which at the end of this timeframe may even challenge the very nature of warfare itself. In this era, no one actor is likely to have any long-term strategic or technological advantage, with aggregate power between the U.S. and its strategic competitors being equivalent, but not necessarily symmetric. Prevailing in this period will depend on an ability to  synchronize multi-domain capabilities against an artificial intelligence-enhanced adversary with an overarching capability to visualize and understand the battlespace at even greater ranges and velocities. Equally important will be controlling information and the narrative surrounding the conflict. Adversaries will adopt sophisticated information operations and narrative strategies to change the context of the conflict and thus defeat U.S. political will.
synchronize multi-domain capabilities against an artificial intelligence-enhanced adversary with an overarching capability to visualize and understand the battlespace at even greater ranges and velocities. Equally important will be controlling information and the narrative surrounding the conflict. Adversaries will adopt sophisticated information operations and narrative strategies to change the context of the conflict and thus defeat U.S. political will.
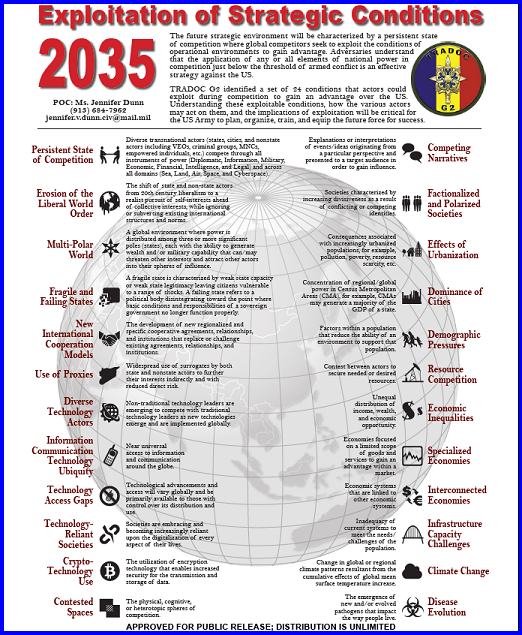
The future strategic environment will be characterized by a persistent state of competition where global competitors seek to exploit the conditions of operational environments to gain advantage. Adversaries understand that the application of any or all elements of national power in competition just below the threshold of armed conflict is an effective strategy against the U.S.

China is rapidly modernizing its armed forces and developing new approaches to warfare. Beijing has invested significant resources into research and development of a wide array of advanced technologies. Coupled with its time-honored practice of reverse engineering technologies or systems it purchases or acquires through espionage, this effort likely will allow China to surpass Russia as our most capable threat sometime around 2030.
China’s Approach to Exploitation
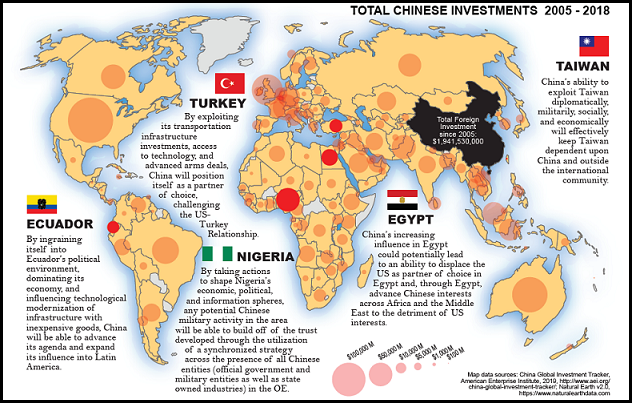
China’s whole-of-nation approach, which involves synchronization of actions across government, military, and industry, will facilitate exploitation of operational environments and enable it to gain global influence through economic exploitation.
China will leverage the international system to advance its own interests while attempting to constrain others, including the U.S.
Preferred Conditions and Methods
The following conditions and methods are conducive to exploitation by China, enabling them to shape the strategic environment in 2035:
-
- Interconnected Economies: China looks for partners and opportunities to become a significant stakeholder in a wide variety of economies in order to capitalize on its investments as well as generate political influence.
-
- Specialized Economies: China looks for opportunities to partner with specialized markets and leverage their vulnerabilities for gain.
-
- Technology Access Gaps: China targets areas where their capital investments in technology provide partners with key resources and competitive advantages by filling technology gaps.
Implications for the U.S. Army:
-
-

The Chinese People’s Liberation Army (PLA) deployed armored medical vehicles and personnel to Germany for the Combined Aid 2019 Joint Exercise with the Bundeswehr this past summer. Traditional Army threat paradigms may not be sufficient for competition.
-
-
- The Army could be drawn into unanticipated escalation as a result of China’s activities during the competition phase.
-
- Army military partnerships will likely be undermined by China in 2035.
-
- Army operations and engagements will be increasingly impacted by the pervasiveness of Chinese goods, technology, infrastructure, and systems.
If you enjoyed this post, please see the original paper and associated infographic of the same title, both by the TRADOC G-2’s Operational Environment and Threat Analysis Directorate and hosted on their All Partners Access Network (APAN) site…
… and read the following MadSci Laboratory blog posts:
A view of the Future: 2035-2050
China’s Drive for Innovation Dominance and Quantum Surprise on the Battlefield?, by Elsa Kania
A Closer Look at China’s Strategies for Innovation: Questioning True Intent, by Cindy Hurst
Critical Projection: Insights from China’s Science Fiction, by Lt Col Dave Calder



 Sea. Per
Sea. Per 



 More information is available than ever before. Recent and extensive developments in technology, media, communication, and culture – such as the advent of social media, 24-hour news coverage, and smart devices – allow people to closely monitor domestic and foreign affairs. In the coming decades, the increased speed of engagements, as well as the precise and pervasive targeting of both civilian and military populations, means that these populations and their respective nations will be even more vulnerable to influence and manipulation attempts, misinformation, and cyber-attacks from foreign adversaries.
More information is available than ever before. Recent and extensive developments in technology, media, communication, and culture – such as the advent of social media, 24-hour news coverage, and smart devices – allow people to closely monitor domestic and foreign affairs. In the coming decades, the increased speed of engagements, as well as the precise and pervasive targeting of both civilian and military populations, means that these populations and their respective nations will be even more vulnerable to influence and manipulation attempts, misinformation, and cyber-attacks from foreign adversaries. The value of influencing and shaping the perceptions of foreign and domestic populations in order to pursue national and military interests has long been recognized. This can be achieved through the employment of information operations, which seek to affect the decision-making process of adversaries. The U.S. Army views information operations as an instrumental part of the broader effort to maintain an operational advantage over adversaries.
The value of influencing and shaping the perceptions of foreign and domestic populations in order to pursue national and military interests has long been recognized. This can be achieved through the employment of information operations, which seek to affect the decision-making process of adversaries. The U.S. Army views information operations as an instrumental part of the broader effort to maintain an operational advantage over adversaries.  The U.S. Army Training and Doctrine Command (TRADOC) G-2’s
The U.S. Army Training and Doctrine Command (TRADOC) G-2’s 
 Russia’s invasion of eastern Ukraine and subsequent annexation of Crimea in 2014 effectively serve as cautionary examples of Russia’s evolving information operations and their perception-shaping capabilities. In Crimea, Russia sought to create a “hallucinating fog of war” in an attempt to alter the analytical judgments and perceptions of its adversaries. With the additional help of computer hackers, bots, trolls, and television broadcasts, the Russian government was able to create a manipulated version of reality that claimed Russian intervention in Crimea was not only necessary, but humanitarian, in order to protect Russian speakers. Additionally, Russian
Russia’s invasion of eastern Ukraine and subsequent annexation of Crimea in 2014 effectively serve as cautionary examples of Russia’s evolving information operations and their perception-shaping capabilities. In Crimea, Russia sought to create a “hallucinating fog of war” in an attempt to alter the analytical judgments and perceptions of its adversaries. With the additional help of computer hackers, bots, trolls, and television broadcasts, the Russian government was able to create a manipulated version of reality that claimed Russian intervention in Crimea was not only necessary, but humanitarian, in order to protect Russian speakers. Additionally, Russian  By denying any involvement in Crimea until after the annexation was complete, distorting the facts surrounding the situation, and refraining from any declaration of war, Russia effectively infiltrated the international information domain and shaped the decision-making process of NATO countries to keep them out of the conflict. NATO nations ultimately chose minimal intervention despite specific evidence of Russia’s deliberate intervention in order to keep the conflict de-escalated. Despite the West’s refusal to acknowledge the annexation of Crimea, it could be argued that Russia achieved their objective of expanding its sphere of influence.
By denying any involvement in Crimea until after the annexation was complete, distorting the facts surrounding the situation, and refraining from any declaration of war, Russia effectively infiltrated the international information domain and shaped the decision-making process of NATO countries to keep them out of the conflict. NATO nations ultimately chose minimal intervention despite specific evidence of Russia’s deliberate intervention in order to keep the conflict de-escalated. Despite the West’s refusal to acknowledge the annexation of Crimea, it could be argued that Russia achieved their objective of expanding its sphere of influence.