[Editor’s Note: Today’s post welcomes back returning guest bloggers Colonel Montgomery Erfourth and Dr. Aaron Bazin, who identify and assess prospective patterns of emerging technology use in the 2020-2027 period by North Korea through the lens of the National Security Strategy and the Special Operations mission. Their assessment offers strategists and planners recommendations on how best to mitigate and address North Korea’s anticipated use of emerging technology against U.S. national interests. Enjoy!]
Introduction
 It has been 75 years since the Korean Peninsula formed into two nations: the Soviet-backed Democratic People’s Republic of Korea (DPRK) and the American-backed Republic of Korea (ROK), commonly referred to as North and South Korea, respectively.1 Since then, North Korea has seen three generations of the ruling Kim Dynasty, become a rogue nation subject to a range
It has been 75 years since the Korean Peninsula formed into two nations: the Soviet-backed Democratic People’s Republic of Korea (DPRK) and the American-backed Republic of Korea (ROK), commonly referred to as North and South Korea, respectively.1 Since then, North Korea has seen three generations of the ruling Kim Dynasty, become a rogue nation subject to a range  of sanctions by the United Nations (UN), and developed nuclear missiles, which it frequently threatens to use.2 While South Korea has flourished economically, the DPRK’s economy has remained stagnant and highly dependent on China, with an unusually high degree of reliance on criminal activity to generate income.3 Recent denuclearization talks between the White House and North Korean leadership, continued U.S. military presence in South Korea, and North Korea’s hostile behavior coupled with their Intercontinental Ballistic Missile (ICBM) and nuclear capabilities are clear signs that the U.S. will remain highly committed to countering the threat from North Korea.4
of sanctions by the United Nations (UN), and developed nuclear missiles, which it frequently threatens to use.2 While South Korea has flourished economically, the DPRK’s economy has remained stagnant and highly dependent on China, with an unusually high degree of reliance on criminal activity to generate income.3 Recent denuclearization talks between the White House and North Korean leadership, continued U.S. military presence in South Korea, and North Korea’s hostile behavior coupled with their Intercontinental Ballistic Missile (ICBM) and nuclear capabilities are clear signs that the U.S. will remain highly committed to countering the threat from North Korea.4
This post explores how North Korea may seek to leverage emerging technologies in the 2020-2027 timeframe to further its national interests, coerce the U.S. into making decisions favorable to North Korea, circumvent sanctions, pose new threats to the Homeland and U.S. interests in the region, and attempt to destabilize international security.
The Third Generation of the Kim Dynasty
North Korea’s current autocratic leader, Kim Jong Un, is the third generation of the Kim Dynasty to declare himself the nation’s supreme leader.5 His father, Kim Jong-Il, allocated most of the national budget to build military capabilities during his reign, with a substantial amount reserved for his ‘gifts’ program to ensure the continuing loyalty of the elite.

Kim Jong Un has continued to prioritize military spending, specifically to develop and expand North Korea’s nuclear capability—he has conducted more missile tests than his father and grandfather combined.6 Simultaneously, increasing malnutrition and disease affect millions of the ‘non-elite’ North Koreans, and between 80,000 and 120,000 political dissidents remain detained in prison camps.7
The DPRK’s leadership has engaged in, and continues to participate in a predictable cycle of provocation with the international community (see figure 1). U.N. sanctions imposed in 2017 in response to these aggressions have markedly affected North Korea’s economy, shrinking its gross domestic product each year and significantly reducing its national revenue streams. In 2018, the country’s international trade fell by 48.4%, and exports were reduced almost 90%.8 Consequently, Kim Jong-Un deviated from previous spending patterns; he reduced spending on the ‘gifts’ program and even confiscated money from elites.9 By January 2020, Kim Jong Un publicly stated that he plans to expand his country’s nuclear force, conduct further nuclear long-range ballistic missile tests, and “find a new way” to bypass sanctions if the United States continues to impose them.10
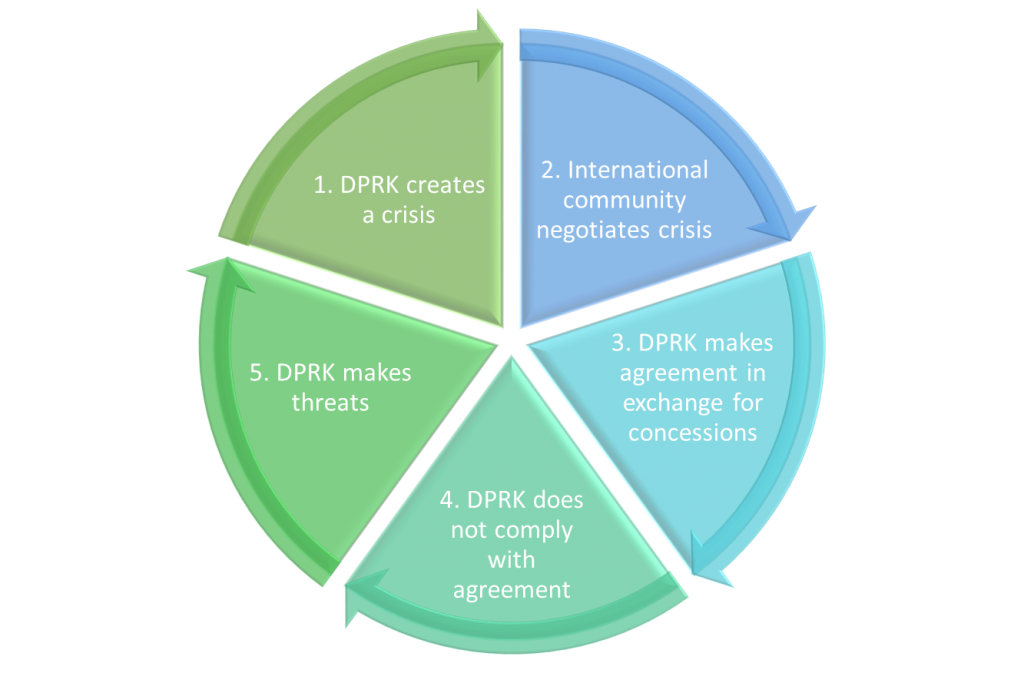
North Korean leadership may seek to leverage emergent technologies as a tool to circumvent the impacts of these sanctions—the “new way” promised by Kim Jong Un. The next section of this post explores how DPRK leadership could leverage five technological developments to harm U.S. security.
Anticipated Technological Developments
Cyber Offensive Actions 2.0
Kim Jong-Il warned his military in 2003 that “If warfare was about bullets and oil until now, warfare in the 21st century is about information.”11 His son has the same appreciation for the information domain and has said, “Cyberwarfare is an all-purpose sword that guarantees the North Korean People’s Armed Forces ruthless striking capability, along with nuclear weapons and missiles.”12 Today, North Korea ranks among the world’s best in offensive cyber operations.13 With the notable Sony hack in retaliation of the Hollywood movie that mocked Kim Jong Un, they have also demonstrated their technical capability and their willingness to retaliate using cyber.14 As North Korea continues to improve its cyber offensive skills, it is likely that in the next seven years it will research the application of AI to automate cyber-attacks,15 such as malware16 and distributed denial-of-service attacks.17

As the U.S. builds its smart infrastructure across industries and further digitizes its economy, it will become increasingly vulnerable to such cyber-attacks in the coming years, creating a space for North Korea to leverage its cyber capabilities to apply pressure on U.S. political leadership. North Korea may continue to develop its cyber offensive capacity, which already has the potential to disrupt critical elements of the U.S. economy and infrastructure. DPRK’s leadership will tailor the use of its cyber capabilities to escalate tensions with the U.S. based on current political events. The SOF community should expand its unconventional warfare and special reconnaissance capabilities to include unique cyber skills that will allow SOF operators to anticipate, deter, and disrupt North Korean cyber-attacks.
Cryptocurrency
Sanctions have severely limited North Korea’s access to the international financial system; as a result, it actively and successfully seeks out other means to generate, collect, and manage revenue streams. The anonymity of cryptocurrency allows North Korea to bypass sanctions, pay for goods and services, and receive money. DPRK has also used stolen cryptocurrency to fund its nuclear weapons program.18 As of 2019, North Korea has taken $2 billion from banks19 and cryptocurrency exchanges20 through cyber-attacks.
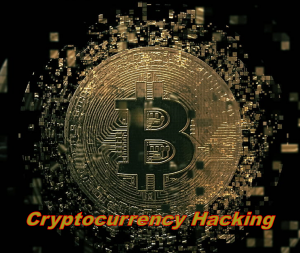 It is highly likely that North Korea will continue to develop its cryptocurrency hacking skills to generate revenue, as this method has already proven to be successful amidst sanctions. As the Department of Defense (DoD) lead for countering illicit finance, the SOF community should develop and further enhance ties with relevant entities in the international community to dismantle illicit financial networks. Two primary entities include the Law Enforcement, Organized Crime, and Anti-Money-Laundering Unit of the United Nations Office on Drugs and Crime,21 and the International Criminal Police Organization (INTERPOL). Domestically, the SOF community should deepen its existing relationship with the U.S. Department of Treasury and expand the scope of its 2013 agreement concerning illicit terrorist financing to include cryptocurrency and North Korea.22
It is highly likely that North Korea will continue to develop its cryptocurrency hacking skills to generate revenue, as this method has already proven to be successful amidst sanctions. As the Department of Defense (DoD) lead for countering illicit finance, the SOF community should develop and further enhance ties with relevant entities in the international community to dismantle illicit financial networks. Two primary entities include the Law Enforcement, Organized Crime, and Anti-Money-Laundering Unit of the United Nations Office on Drugs and Crime,21 and the International Criminal Police Organization (INTERPOL). Domestically, the SOF community should deepen its existing relationship with the U.S. Department of Treasury and expand the scope of its 2013 agreement concerning illicit terrorist financing to include cryptocurrency and North Korea.22
The Dark Web
North Korea actively engages in illicit finance and sells drugs23 and military arms,24 three activities that are prolific on the Dark Web. As discussed in the previous section, the DPRK uses cryptocurrency to bypass the international financial system. While their equipment is subject to embargos, they can conduct cyber arms purchases and sales with relatively few barriers on the Dark Web.25 If left unchecked, it is likely they will also leverage the platform with impunity to sell drugs (predominantly crystal meth26), engage in illicit finance, and further their criminal enterprise.27
 The SOF community should create a coordinated and ongoing Dark Web collaborative information-sharing agreement with USSCYBERCOM and relevant Intelligence Community (IC) stakeholders. Given the types of activity conducted on the Dark Web—namely narcotics sales, money laundering, and weapons of mass destruction proliferation—this intelligence would also be useful for other SOF missions outside the Korean Peninsula. It may also have secondary uses in support of SOF psychological operations in the region.
The SOF community should create a coordinated and ongoing Dark Web collaborative information-sharing agreement with USSCYBERCOM and relevant Intelligence Community (IC) stakeholders. Given the types of activity conducted on the Dark Web—namely narcotics sales, money laundering, and weapons of mass destruction proliferation—this intelligence would also be useful for other SOF missions outside the Korean Peninsula. It may also have secondary uses in support of SOF psychological operations in the region.
Additive Manufacturing
Additive manufacturing, also known as three-dimensional (3D) printing, allows anyone with a 3D digital file (or the software to make one) to print designs into physical form. This form of independent manufacturing caught the eye of North Korean leadership when they explored its use in medicine and dentistry.28 It is highly likely that since then, North Korean engineers have been exploring 3D printing use-cases to manufacture weapons29 and develop atomic arsenals with smaller nuclear payloads, giving them asymmetric capabilities able to undermine U.S. conventional military advantages.30 In addition, when combined with advances in AI, additive manufacturing could make it easier for nations to build chemical and biological weapons covertly.31
 The authors expect that DPRK will seek to leverage 3D printing to bypass military-related economic sanctions; reduce the costs, staffing, and length of development cycles required for new arms; and bolster their nuclear capabilities. To deny, degrade, disrupt, or destroy North Korea’s capabilities to 3D-print nuclear, chemical, and biological weapons, the SOF community should coordinate with the Target Office of Primary Interest to understand how SOF operators could best achieve the desired end state for this problem set.
The authors expect that DPRK will seek to leverage 3D printing to bypass military-related economic sanctions; reduce the costs, staffing, and length of development cycles required for new arms; and bolster their nuclear capabilities. To deny, degrade, disrupt, or destroy North Korea’s capabilities to 3D-print nuclear, chemical, and biological weapons, the SOF community should coordinate with the Target Office of Primary Interest to understand how SOF operators could best achieve the desired end state for this problem set.
Unmanned Aerial Vehicles (UAVs) & Autonomous Underwater Vehicles (AUVs)
UAVs and AUVs can carry and deliver chemical, biological, radiological, and nuclear (CBRN) payloads. There is “consensus that the Korean People’s Army  (KPA) possesses mustard, phosgene, blood agents, sarin, tabun, and V-agents (persistent nerve agents).”32 Sources consistently cite that North Korea possesses “13 types of biological agents including anthrax and the plague” and the capability to weaponize them.33 The use of CBRN payloads in drones would have grave repercussions, especially for U.S. forces in South Korea or South Korean targets.34 IF North Korea pursues the employment of existing chemical and biological assets35 using UAVs and AUVs, they may use this capability as a form of coercion to improve its negotiating position.
(KPA) possesses mustard, phosgene, blood agents, sarin, tabun, and V-agents (persistent nerve agents).”32 Sources consistently cite that North Korea possesses “13 types of biological agents including anthrax and the plague” and the capability to weaponize them.33 The use of CBRN payloads in drones would have grave repercussions, especially for U.S. forces in South Korea or South Korean targets.34 IF North Korea pursues the employment of existing chemical and biological assets35 using UAVs and AUVs, they may use this capability as a form of coercion to improve its negotiating position.
This section highlighted the anticipated technologies that North Korea may seek to leverage in the 2020-2027 period—including the most probable use-cases and the threats they pose to U.S. national security interests—and a recommended course of action for SOF to mitigate risk. The next section assesses the North Korean challenge from a strategic perspective and provides recommendations to counter current and future North Korean aggression.
Strategic Opportunities and Recommendations
SOF-Supported Coordinated Messaging
The SOF community should create an enhanced working group to coordinate messaging more effectively. Consistent and sustained coordinated themes and messages will help manage malign behavior by the DPRK, drive narratives that support U.S. interests, counter North Korean negative messaging, and support diplomatic efforts made by U.S. senior political leadership. This working group should include representatives from the State Department’s Global Engagement Center and the Treasury Department, White House security advisors on North Korea, the State Department head for North Korean affairs, and relevant civilian partners.
Leveraging SOF Authorities and USCYBERCOM Capabilities
Evidence suggests that North Korea will continue to use cyber tools to achieve effects that drive geopolitical outcomes. Politically, there is a delicate balance between rhetorical escalation and the display of military force. The DPRK has used offensive cyber actions to bypass sanctions in the past and will most likely continue to do so.
 As the DoD lead for counter-threat finance, the SOF Community should leverage the information operations capabilities of USCYBERCOM to offer political leadership options for nuanced forms of escalation, alternative ways of signaling, and other political actions.
As the DoD lead for counter-threat finance, the SOF Community should leverage the information operations capabilities of USCYBERCOM to offer political leadership options for nuanced forms of escalation, alternative ways of signaling, and other political actions.
The SOF enterprise’s global reach makes continuous information watch and response possible, and this persistent engagement should support efforts for the more significant DoD Cyber Strategy36 of ‘defending forward.’ The Joint Military Information Support Operations WebOps Center should construct and guide messaging in a synchronized fashion and mitigate the adverse effects of information attacks and narratives with an immediate and coherent response—especially during the early stages of the DPRK’s provocation cycle. Simply put, this could reduce the likelihood of conflict and reduce the negative ramifications should a strategic miscalculation occur.
Cyber Foreign Internal Defense (FID)
South Korea is an important ally whose history and geographic proximity to the DPRK present a high degree of risk. It is also a highly-developed, industrialized country with a significant digital presence. Accordingly, they are a prime candidate  for U.S. FID that focuses on countering North Korean cyber aggression. As such, the SOF community should further deepen U.S.-ROK cyber collaboration and capabilities. USSCYBERCOM owns the global mission for cyber, while SOF’s primary mission in FID is to assess, train, advise, and assist host nation military and paramilitary forces. Accordingly, these Combatant Commands should work together to determine the optimal command relationship for the Cyber-FID mission.
for U.S. FID that focuses on countering North Korean cyber aggression. As such, the SOF community should further deepen U.S.-ROK cyber collaboration and capabilities. USSCYBERCOM owns the global mission for cyber, while SOF’s primary mission in FID is to assess, train, advise, and assist host nation military and paramilitary forces. Accordingly, these Combatant Commands should work together to determine the optimal command relationship for the Cyber-FID mission.
Conclusion
North Korea will continue to exploit new technologies that serve their interests while keeping its critical infrastructure disconnected from the open internet. This protects them from retaliatory cyber-attacks and requires the U.S. to identify alternative means of response. Recent diplomatic overtures have ended without resolution, and the DPRK’s cycle of aggression continues. Looking forward, North Korea will most likely expand its exploitation of cryptocurrencies, cyber hacking capabilities, and investments in other emerging technologies to preserve its regime.
As the U.S. seeks to harness the power of these new technologies—such as digitizing critical infrastructure and standing up smart cities—growing connectivity increases vulnerabilities. North Korea will most likely seek to gain an advantage and free itself from confining economic sanctions by bolstering its asymmetric toolset; the ‘all-purpose sword’ of cyber may become its most reliable and effective tool. By coordinating messaging, exploring cyber FID, and leveraging relationships, SOF can create a range of options that give the U.S. a strategic advantage for America’s security posture in the region. Applied correctly, these new options have the potential to help SOF in its ultimate goal: to advance and defend U.S. interests abroad.
If you enjoyed this post, read the following:
Extremism on the Horizon: The Challenges of VEO Innovation, by Colonel Erfourth and Dr. Bazin
A New Age of Terror: The Future of CBRN Terrorism, by Mr. Zachary Kallenborn
Army Installations: A Whole Flock of Pink Flamingos by Dr. Jason R. Dorvee, Mr. Richard G. Kidd IV, and Mr. John R. Thompson
… and check this out: The U.S. Army’s Mad Scientist Initiative is partnering with the National Security Innovation Network (NSIN) to explore solutions to problems in the Dense Urban space. This online challenge is open to anyone and everyone, inside and outside of the DoD. Click here for more information on this virtual game, which starts on 1 May 2020. The solutions and ideas you come up with might even earn you the chance to compete at our in-person hackathon in NYC!
About the Authors:
Colonel Montgomery Erfourth is currently the Integration Division Chief with the J5 at U.S. Special Operations Command in Tampa, Florida. He has over 25 years of professional military and civilian experience in the areas of leadership, planning, strategy, research, transportation, supply chain management, marketing, budget, and financial management. Monte has worked closely with U.S. Ambassadors, highest level of military leadership, and policy makers and performed duties in over 25 countries, several of which were in non-permissive environments.
Dr. Aaron Bazin adds value to organizations by helping them explore the possibilities of the future and develop unique, visionary strategies. He is a skilled researcher, facilitator, presenter, and writer. Aaron is currently the Managing Director of the Donovan Strategy and Innovation Group, U.S. Special Operations Command in Tampa, Florida. His team acts as catalyst for change and innovation across the Joint SOF enterprise to improve its ability to further national interests globally.
Disclaimer:
The views expressed in this blog post are solely those of the authors and do not necessarily reflect those of the Department of Defense, U.S. Special Operations Command, Department of the Army, Army Futures Command, or the Training and Doctrine Command.
1 History. (2018). North Korea. History. https://www.history.com/topics/korea/north-korea-history
2 Panda, Ankit, Naarang, Vipin. (2019). Why North Korea Is Testing Missiles Again: Is a Much Larger Escalation on the Horizon? Foreign Affairs. https://www.foreignaffairs.com/articles/north-korea/2019-05-16/why-north-korea-testing-missiles-again
3 Perez, Evan., Shortell, David. (2019). North Korean-backed bank hacking on the rise, US officials say. CNN. https://edition.cnn.com/2019/03/01/politics/north-korea-cyberattacks-cash-bank-heists/index.html
4 White House. (2019). President Donald J. Trump Is Strengthening Our Historic Alliance with the Republic Of Korea. White House Foreign Policy. https://www.whitehouse.gov/briefings-statements/president-donald-j-trump-strengthening-historic-alliance-republic-korea/
5 Biography. (2019). Kim Jong-Un Biography. https://www.biography.com/dictator/kim-jong-un
6 Albert, Eleanor. (2019). What to Know About Sanctions on North Korea. Council on Foreign Relations. https://www.cfr.org/backgrounder/what-know-about-sanctions-north-korea
7 Nebehay, Stephanie. (2019). North Korea maintains repression, political prison camps: U.N. expert. World News. Reuters. https://www.reuters.com/article/us-northkorea-rights-un/north-korea-maintains-repression-political-prison-camps-u-n-expert-idUSKBN1QP28J
8 Yoo, Choonsik. (2019). North Korea’s economy tanks as sanctions, drought bite: South Korea. Reuters. https://www.reuters.com/article/us-northkorea-economy-gdp/north-koreas-economy-tanks-as-sanctions-drought-bite-south-korea-idUSKCN1UL08G
9 Lee, Christy. (2019). Sanctions Threaten North Korea’s Old and New Elites. https://www.voanews.com/east-asia-pacific/sanctions-threaten-north-koreas-old-and-new-elites
10 Sang-hun, Choe. (2020). What Kim Jong-un’s Latest Threats Say About His Trump Strategy. NY Times. https://www.nytimes.com/2020/01/01/world/asia/north-korea-kim-trump.html
11 Sanger, David., Kirkpatrick, David., Perlroth, Nicole. (2017). The World Once Laughed at North Korean Cyberpower. No More. The New York Times. https://www.nytimes.com/2017/10/15/world/asia/north-korea-hacking-cyber-sony.html
12 Kong, Ji Young., Lim, Jong In., Kim, Kyoung, Gon. (2019). The All-Purpose Sword: North Korea’s Cyber Operations and Strategies. 2019 11th International Conference on Cyber Conflict. https://ccdcoe.org/uploads/2019/06/Art_08_The-All-Purpose-Sword.pdf
13 Tai, Crystal. (2019). North Korean cyberwarfare: as big a threat as its nuclear weapons?. South China Morning Post. https://www.scmp.com/week-asia/geopolitics/article/2187363/north-korean-cyberwarfare-big-threat-its-nuclear-weapons
14 U.S. Department of Justice. (2018). North Korean Regime-Backed Programmer Charged With Conspiracy to Conduct Multiple Cyber Attacks and Intrusions. The United States Department of Justice. https://www.justice.gov/opa/pr/north-korean-regime-backed-programmer-charged-conspiracy-conduct-multiple-cyber-attacks-and
15 King, Meg., Rosen, Jacob. (2018.) The Real Challenges of Artificial Intelligence: Automating Cyber Attacks. Wilson Center. https://www.wilsoncenter.org/blog-post/the-real-challenges-artificial-intelligence-automating-cyber-attacks
16 Conran, Matt. (2018). The rise of artificial intelligence DDoS attacks: The leaves may change color, but the roots are the same. Are you ready for AI-based DDoS attacks?. Network World. https://www.networkworld.com/article/3289108/the-rise-of-artificial-intelligence-ddos-attacks.html
17 Stone, Mark. (2018). Fight Fire With Fire: How AI Plays a Role in Both Stopping and Committing DDoS Attacks. Security Intelligence. https://securityintelligence.com/fight-fire-with-fire-how-ai-plays-a-role-in-both-stopping-and-committing-ddos-attacks/
18 Burgess, Matt. (2019). North Korea’s elite hackers are funding nukes with crypto raids. Wired. https://www.wired.co.uk/article/north-korea-hackers-apt38-cryptocurrency
19 Orcutt, Mike. (2019). North Korea is funding its weapons program with stolen cryptocurrency. MIT Technology Review. https://www.technologyreview.com/f/614149/north-korea-is-funding-its-weapons-program-with-stolen-cryptocurrency/
20 Nichols, Michelle. (2019). North Korea took $2 billion in cyberattacks to fund weapons program: U.N. report. Reuters. https://www.reuters.com/article/us-northkorea-cyber-un/north-korea-took-2-billion-in-cyberattacks-to-fund-weapons-program-u-n-report-idUSKCN1UV1ZX
21 UNODC. (2019). UNODC on money-laundering and countering the financing of terrorism. https://www.unodc.org/unodc/en/money-laundering/
22 INTERPOL. (2019). Tracing Terrorist Finances. INTERPOL. https://www.interpol.int/en/Crimes/Terrorism/Tracing-terrorist-finances
23 Kwong, Jessica. (2018). North Korea Could Become Leading Supplier of Crystal Meth, Fake Bitcoin following Sanctions, Expert Warns. Newsweek. https://www.newsweek.com/north-korea-could-deal-crystal-meth-and-sell-counterfeit-cryptocurrency-due-783697
24 CIA. (2009). North Korean activities Overseas: A Research Paper. Central Directorate of Intelligence. https://www.cia.gov/library/readingroom/docs/CIA-RDP85T00310R000200050003-7.pdf
25 Rivera, Jason., Archy, Wanda. (2018). The Role of the Dark Web in Future Cyber Wars to Come. Small Wars Journal. https://smallwarsjournal.com/jrnl/art/role-dark-web-future-cyber-wars-come
26 BBC. (2015). https://www.bbc.co.uk/programmes/p030zj27r
27 Gollom, Mark. (2017). Drugs, counterfeiting: How North Korea survives on proceeds of crime. CBC News. https://www.cbc.ca/news/world/north-korea-criminal-empire-drugs-trafficking-1.4435265
28 Byrne, Leo. (2016). North Korea shows 3D printer for cosmetic, dental use. NK News. https://www.nknews.org/2016/08/north-korea-shows-3d-printer-for-cosmetic-dental-use/
29 3D Natives. (2017). North Korea could use 3D printing to manufacture weapons. https://www.3dnatives.com/en/north-korea-3d-printing250820174/
30 Wichner, David. (2015). Raytheon looks to 3D printing for missiles Company can print up to 80 percent of a missile’s parts. Security Info Watch. https://www.securityinfowatch.com/security-executives/news/14065439/raytheon-looks-to-3d-printing-for-missiles
31 Gault, Matthew. (2019). 3-D Printers Could Help Spread Weapons of Mass Destruction: Experts warn that new technology makes it easier to covertly produce WMDs. Scientific American. https://www.scientificamerican.com/article/3-d-printers-could-help-spread-weapons-of-mass-destruction/
32 International Crisis Group. (2009). North Korea’s Chemical and Biological Weapons Programs. https://www.crisisgroup.org/asia/north-east-asia/korean-peninsula/north-korea-s-chemical-and-biological-weapons-programs
33 Kim, Hyun-Kyung., Philipp, Elizabeth., Chung, Hattie. (2019). North Korea’s Biological Weapons Program: The Known and Unknown. Project on managing the Microbe. Belfer Center for Science and International Affairs. Harvard Kennedy School. https://www.belfercenter.org/sites/default/files/2017-10/North%20Korea%20Biological%20Weapons%20Program.pdf
34 Mizokami, Kyle (2019). Forget About North Korea’s Nukes: Fear Kim’s Chemical Weapons. The National Interest. https://nationalinterest.org/blog/buzz/forget-about-north-koreas-nukes-fear-kims-chemical-weapons-48152
35 NTI (2018). North Korea: Chemical. https://www.nti.org/learn/countries/north-korea/chemical/
36 DoD. (2018). Summary: Department of Defense Cyber Strategy https://media.defense.gov/2018/Sep/18/2002041658/-1/-1/1/CYBER_STRATEGY_SUMMARY_FINAL.PDF




North Koera has always been about applying the cheapest means to prop up all aspects of its elite classes in suppression of its common classes and give the outward appearance of being ‘backward’ and ‘low tech’ externally while internally showing it can compete in the modern world.
Every item of manufacture will have the ability to be ‘spun’ politically, militarily, economicly, societally, infrastructurally, informationally and have at least two or three uses (physically), the first being an internal use (to supress the people to keep them in abject fear of the state, the embodiment of which is the Kim dynasty of ‘living gods’), and an external use (to appear strong in the face of Western advances, privlage, indulgance, excesses, waste, thusly reinforcing Kim mantras of juche, songun and now byeongjin). 3rd option uses include strengthing a hold on power by the Kims (or a ‘Kim’), making money regardless of how small a margin of profit or success (thus making the DPRK more a criminal enterprise), and if the cheap option can do the most, run with it until the perceived threat (be it an internal or external) can counter it or suppress it.
It just happens that geographically, its two largest neighbors (Russia and China) will play off each other to include North Korea, so they have a three ring circus of geo-political dependancy all rooted in each others own form of Marxism (Russian focus on Communism flavored democracy, China focus on Communist Mao flavored Confusionism…which is very flexible and adoptive as long as its dressed in ‘Maoisms’, and North Korea on Stalin based-dynastic Facism) and need to keep each other at just enough arms distance (because they can’t trust each other in the darkest of hearts) but close enough to appear united in responding to perceived threats from the West (to inlcude Japan and South Korea because they are considered too influenced by Europe and North America).